Are you worried about your documents being targeted with the Cryptolocker Virus or a similar type of Trojan Horse ransomware? That’s completely understandable, and you are not the only attorney who’s worried about this.
· Global BigLaw Firm Paralyzed by New Ransomware Attack
· Hackers lock law firm files for three months with ransomware
· Ransomware’ software attacks stymie law firms
Malware attacks are a part of the digitalization of information. They’re not going away anytime soon.
But that doesn’t mean we have to put up with them or risk confidentiality or financial security in our law firms.
In fact, there are some easy things we can do to protect our documents. This article covers what ransomware is, how it works, and a simple way you can prevent ransomware from stealing your valuable information…
How damaging ransomware is and how it affects law firms
Ransomware is especially nerve-wracking to deal with because it can bring your entire workday to a stop by hitting your master boot record and making your computer unusable.
Attackers who use ransomware are looking for exactly what the name implies— a ransom. They will often attempt to make you pay them a specific sum of money to get your system back in working order. They are holding your business for ransom.
How ransomware works
Here’s the step-by-step of what happens when you get hit with ransomware:
● You or someone in your office unwittingly click on an attachment infected with ransomware, such as in a phishing email that fools you into clicking a scam link.
● The ransomware then crawls your computer, finding all the network drives and encrypting those files.
● If you have a file synchronization tool like Dropbox or Google Drive, the ransomware will encrypt those files on your computer, which will sync up with the cloud and then sync back down to other computers on your network that have Dropbox or Google Drive synced.
● You have to decide whether to pay the ransom or wipe everything and restore from backups. Regardless of your decision, your office is going to be down for some time.
When it’s all said and done, every computer on your network could become unusable until the ransomware is removed.
You can’t get ransomware with NetDocuments
Unlike Dropbox and Google Drive, NetDocuments is a true* cloud-based document management system, where all of your documents reside on NetDocuments servers.
When you open up a file from NetDocuments it downloads to your computer, you make changes, and then it goes back into NetDocuments.
So if you are using NetDocuments and you accidentally install ransomware, there are no mapped network drives to encrypt and spread the virus.
ndSync
The only exception would be NetDocuments users that have installed ndSync. ndSync is Dropbox for NetDocuments. It allows users to sync certain folders or documents on their local computer. Now, if you have ndSync installed and get ransomware, the files on your local computer could get infected; however, that is why NetDocuments has developed the Circuit Breaker function.
Circuit Breaker tracks local activity being synced to NetDocuments and will suspend document syncing if it detects behavior that resembles ransomware. With all these protections in place, it makes sense to utilize the software tools that can best prevent ransomware from bringing your law firm to a halt. If you don’t want to get ransomware, move to NetDocuments.
*True Cloud
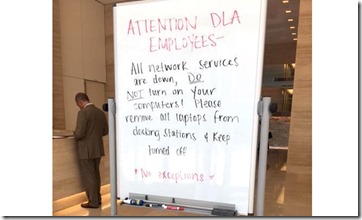
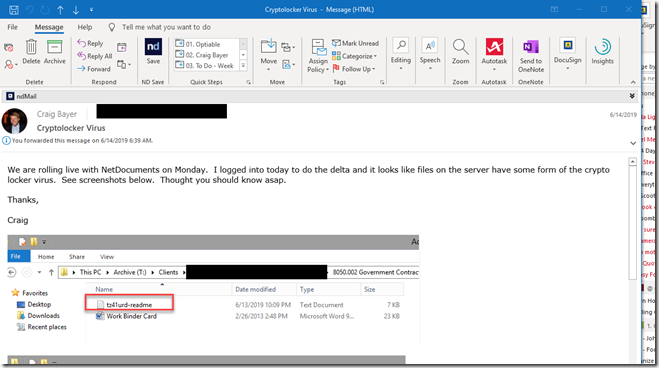
There were a lot of companies that thought the cloud was a fad and decided to keep developing on-premise software. Once they realized that everything was moving to the cloud, they were in trouble. Most of them decided to start housing Windows Servers with their products installed on them. Users could then remote into those computers, and they could claim they had a cloud product. Those remote servers can easily get ransomware. One of them did in the middle of a NetDocuments migration: