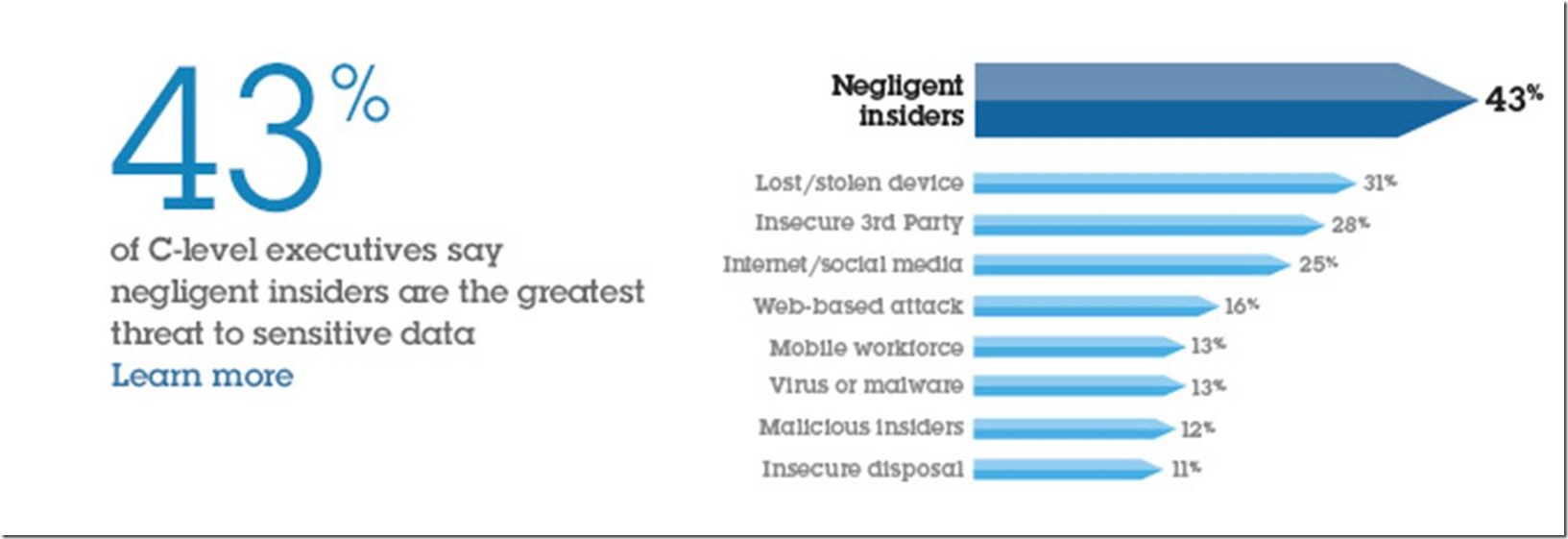
Forty-three percent of C-level executives say their biggest security threat is negligent insiders or employees*.
*http://www-935.ibm.com/services/hk/en/it-services/data-breach/data-breach-statistics.html
The keyword here is ‘negligent’, meaning they accidentally screwed up. The next threat is a lost or stolen device. In the US alone, people lose about 12,000 laptops a week in airports, which comes to around 600,000 a year. http://www.ponemon.org/news-2/8
In the past, this was never an issue. All work was stored in the office. Now company data resides on multiple devices at the home and office. Some data might even be on a device not owned by the company.
We refer to this trend as Bring Your Own Device or BYOD. Fewer companies are supplying smartphones to their employees because most people already have one. The same thing is happening with tablets and laptops.
This new shift requires a couple of new steps to safeguard our data.
1. Have a Policy
When someone starts working for you, that employee should sign a policy stating that the company owns the entire work product regardless of it being stored on a personal device or a company device. The policy also needs to include things like:
- Password Length and Complexity for personal devices that store company data
- Smartphone / Tablet Pin Password Requirements
- Antivirus required for personal computers
- Data Encryption requirements
- Whether they can use DropBox or Google Drive
For a good example, see: http://www.itmanagerdaily.com/byod-policy-template/
2. Turn on Email Archiving
Having a policy is a good first step, but we also need to maintain a Trust but Verify approach.
The three most popular email providers for companies are Microsoft Exchange (server in your office) Microsoft 365 (server in the cloud) and Google Apps (Gmail for business).
If you have any of these three, you have the ability to turn on email archiving, which preserves all email, regardless if the user deleted it.
Turn on Email Archiving:
- ·Google Apps: https://support.google.com/a/answer/151128?hl=en
- Microsoft 365: https://products.office.com/en-us/exchange/microsoft-exchange-online-archiving-email
- Exchange: https://technet.microsoft.com/en-us/magazine/hh875169.aspx
3. Disable Accounts
We often get phone calls like the following “Hey, we have a new employee. Will you set them up?” My immediate reply is “Okay, who are they replacing?” “Oh, Matt. He left two months ago.”
The problem is all of Matt’s accounts are still active and no one bothered to disable anything.
This was easy before the internet, just take away the person’s office key and they cannot get any data.
At my office, we have a checklist that lists all the things we need to change when someone leaves:
- Redirect the Email Account and Change the Password
- Disable NetDocuments User Account (document storage)
- Disable BrainKeeper User Account (company knowledgebase)
- Disable Basecamp User Account (project management)
- Disable Autotask User Account (CRM and Client Data)
- Disable access to the Optiable Website
- Change the Optiable Twitter Account Password
- Change Office Wi-Fi Password
If somebody has given their notice and they are coming up on their last couple of days, have a policy or checklist in place to disable all of these accounts.
4. Protect Wi-Fi Networks
The wireless router in your office should have two networks, the regular one and the guest network. Anyone on the guest network can browse the internet but cannot see any computers on the network.
A lawyer I knew got an ethics complaint filed against him. A disgruntled employee was driving to the office parking lot at night, connecting to the firm’s Wi-Fi network, and sending threatening emails to a judge, using a fake Gmail account. The court ran a reverse lookup on the email and discovered that it came from the attorney’s office and assumed it was him. The firm had a password on their Wi-Fi, but they did not change it when they fired this person. So, change your Wi-Fi passwords when you let someone go.
5. Use Document Management Software (DMS)
There is a variety of reasons to do this, but we are just going to concentrate on the security aspects. A good DMS will do the following:
- Prevent employees from deleting documents and emails.
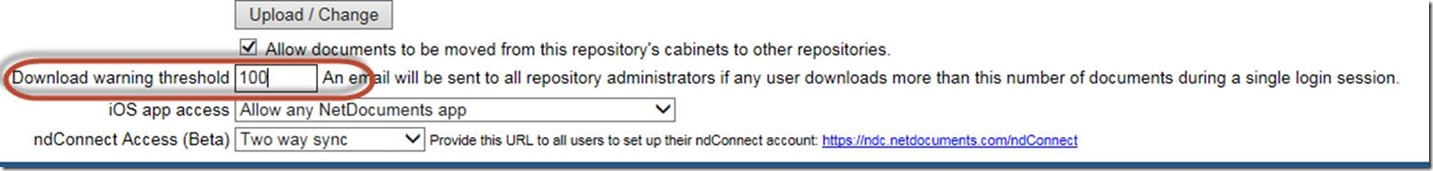
- Prevent employees from coming in at night and copying all the firm’s documents.
- Give you a history of every document a user has read, copied and edited.
NetDocuments and Worldox are very popular for these reasons.
If your documents are on a server at your office, it is extremely easy for anyone to plug in a USB hard drive and copy thousands of documents off the system. A DMS can help prevent this from happening and provide a detailed report of a user’s activity.
6. Mobile Device Management
If you read the news, you are aware of the battle between the FBI and Apple over the ability to unlock a terrorist’s iPhone. What I found interesting is that the terrorist’s employer owned the phone, but put no Mobile Device Management software on it.
This is software that when installing on a smartphone, gives the business complete control over the device. You would be able to unlock and employee’s phone and could restrict access to certain apps. Software like Air-Watch costs about $9 a month for control of 3 devices and scales up from there.
Companies cannot supply devices to their employees without installing Mobile Device Management software.
If you are going to let employees bring their own equipment, you can still use products like Air-Watch to protect the company data on your employee’s equipment.