Companies and individuals are often targeted by hackers via spoof emails that are cleverly designed to look they were sent by a legitimate bank, government agency, or another official organization.
Initially, they seemed fairly easy to spot, but unfortunately, today, it can be difficult to distinguish a spoof email from a genuine one.
However, most spoof emails feature subtle signs of dishonesty, and if you know what to look out for, they can be easy to spot.
That’s where we come in to help. Here are the spoof email signs to watch out for so you can maintain your law firm security and avoid being fooled by malicious emails.
What Are the Goals of Spoof Emails?
There are two reasons why cybercriminals distribute spoof emails.
The first is to trick individuals into giving away personal information, such as their username and password. This technique is called phishing.
The second is to con individuals into downloading a virus or malware. Once this malware is installed into a device, hackers can use it to steal sensitive data.
How to Spot a Spoof Email
If you’re wary of an email and it displays any of the following signs, then it could be a spoof email. You should delete it right away and block the email address from sending you any further scam emails.
Bad Spelling and Grammar
The easiest way to recognize a spoof email is bad grammar. Any legitimate organization will send an email that is well-written and has been proofread.
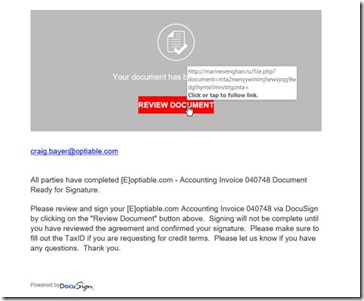
Generic Greetings
If a suspicious email starts with a generic greeting – beware! A generic greeting can be anything from ‘Dear Sir or Madam’ to ‘Dear valued member,’ ‘Dear account holder,’ or ‘Dear customer.’
Any legitimate company that requires information regarding your account will call you by name and would probably require you to speak to them via the phone.
However, some scammers have learned to avoid a greeting altogether, so be aware of this trend. This is especially common with emails that display advertisements, so these phishing emails can be more difficult to spot.
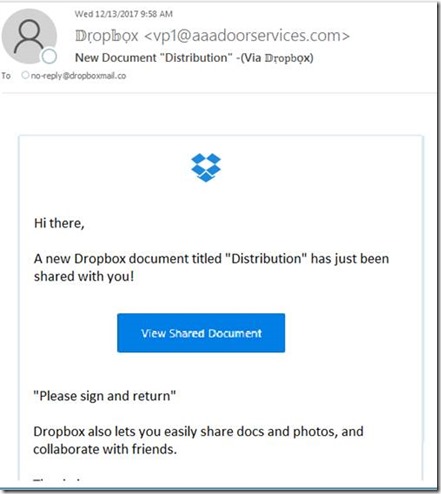
The Company Name Doesn’t Match the Domain Name
Don’t just check the name of the person sending you an email but check their email address too. If it isn’t displaying directly, hover your mouse over the ‘from’ address, and it should pop up.
A phishing email address will look different from a genuine one. For example, amy@paypal.com would be a genuine email compared to amy@paypal123.com, which would be a phishing email.
Just remember to take this point with a grain of salt. Some companies use unique or varied domains to distribute emails, while others use third-party email providers.
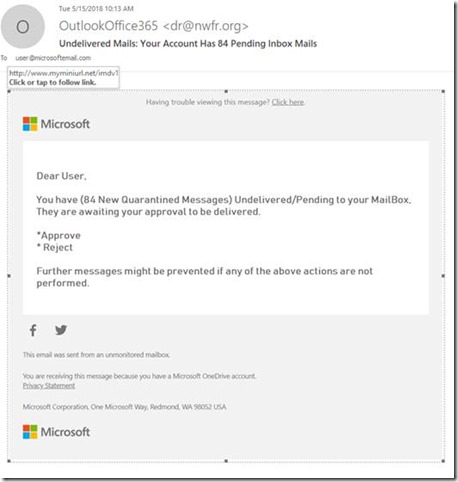
The Link in the Email Doesn’t Match the Domain Name
Likewise, if the link in the email doesn’t match the domain name, then it may well be a spoof email.
Double-check the URLs that feature in an email. If the link in the text doesn’t match the URL displayed when the cursor hovers over the link, it’s an obvious sign of a phishing email. Don’t click on it!
Use of Link Shorteners
Link shorteners like Tiny URL or bit.ly are very used when you need to send a long web address to someone. They are also a great way for someone to disguise where a website is sending you. Most phishing emails use link shorteners.
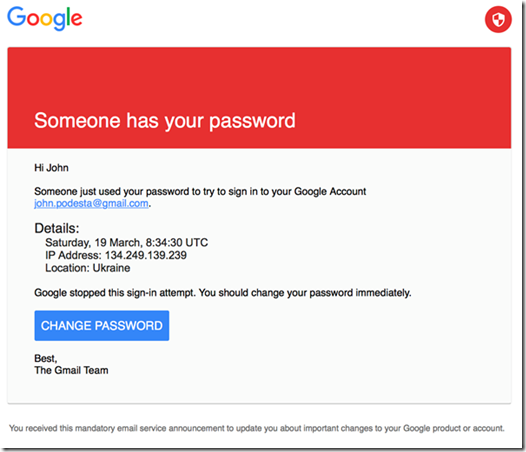
Email Requests a Password Reset
If the suspicious email in question suggests clicking onto a link for you to reset your password, this is a big sign that it’s a phishing email. If you don’t remember requesting a password reset from a company, then it’s unlikely they’d contact you to.
If you feel the need to reset your password, manually log into the website and reset your password. Never click on a link in an email to do so.
Staying Safe
It doesn’t matter if your company has the most secure email security system; it just takes one untrained employee to be fooled by a spoof email and accidentally gives away valuable data.
Make sure all your employees understand these signs of email phishing so your company can stay protected.